| |
|
|
| |
|
|
|
 |
|
| |
|
Fwd: Security Alert
Bank of America
|
|
|
|
 |
|
 |
| |

|
Date Reported: 1st February 2011  |
Risk Level: MEDIUM  |
|
| |
 |
 |
| |
Email Subject: |
Fwd: Security Alert |
|
Apparent Sender: |
Bank of America  |
|
Return Address: |
Not found  |
|
| Email Format: |
HTML  |
| |
URL of Web Content: |
http://alert_account_0nl1neast.t35.com/account_sum
mary/index.html
 |
|
Anchor text of URLs: |
1) URL link is in form of image, 2) Sign in
to Online Banking, 3) Sign in to Online
Banking  |
|
Location: |
Location not available  |
| |
Scam number: |
15481-221245-507145 |
| |
Comments: |
- Email asks you to confirm/update/verify your account data at Bank of America by visiting the given link. You will be taken to a spoof website where your details will be captured for the phishers.
- Bank of America never send their users emails requesting personal details in this way.
- The spoof website this email links to was not online at time of this report, but variations of the scam which link to working websites are bound to exist, so be wary! The website may have been taken down or disabled by the hosts, but quite often these websites are hosted on the personal computer of the phishers, so may only be online at certain times.
|
| |
|
|
 |
 |
| |
|
| |
Return-path: Envelope-to:
spoof@millersmiles.co.uk Delivery-date: Mon,
31 Jan 2011 15:47:39 +0000 Received: from
vms173005pub.verizon.net
([206.46.173.5]:44566) by
server5.webserver25.net with esmtp (Exim
4.69) (envelope-from ) id
1Pjvyd-0007OD-HL for
spoof@millersmiles.co.uk; Mon, 31 Jan 2011
15:47:39 +0000 Received: from
vms232.mailsrvcs.net
([unknown] [192.168.1.2]) by
vms173005.mailsrvcs.net (Sun Java(tm) System
Messaging Server 7u2-7.02 32bit (built Apr 16
2009)) with ESMTPA id...
|
|
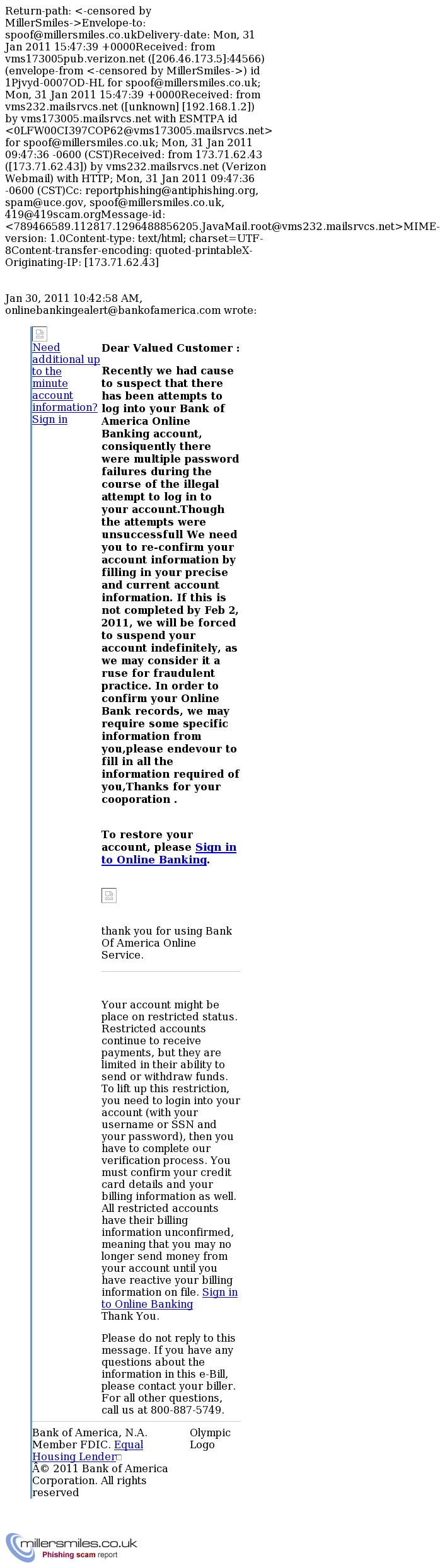
Click for full size image |
| |
| Website: |
|
|
| |
|
| Website was not online when we checked. It returned the error 403 |
|
|
 |
 |
 |
|
| |
 See our most recent scam reports See our most recent scam reports |
 |
Browse our scam report archives |
 |
Search |
Please send us any scam/phishing emails you have received by reporting them here
For access to our huge blacklist of domain names and to sign up to our live feed of ALL the scams we receive please take a look at our Honeytrap service
If you have received the email below, please remember that it is very common for these email scams to be redistributed at a later date with only slightly different content, such as a different subject or return address, or with the fake webpage(s) hosted on a different webserver.
We aim to report every variant of the scams we receive, so even if it appears that a scam you receive has already been reported, please submit it to us anyway.
|
| |
|
|
|
|